HELPING SMALL BUSINESSES SUCCEED
MORE DONUTS:
What do you need to know about small business tech?
Get the right hardware, tech and devices to make running your business easy.
Also in this topic
Essential software and apps for small businesses from accounts and finance software to payroll and CRM.
Also in this topic
Get your business online. Build a website, sell online, store data and benefit from cloud services.
Also in this topic
Stay in touch with customers, staff and suppliers - email, phone, collaboration and conferencing tools.
Also in this topic
Keep your systems running smoothly by protecting your IT, data and systems.
Also in this topic
Identity your IT needs, set a budget, choose suppliers and buy the IT you need for business success.
Also in this topic
IT support options for small businesses from in-house support to outsourced technical support.
Also in this topic
IT training and policies help you get the most of your IT - boosting productivity and reducing errors.
Also in this topic
Tech blog
Latest blogs
Intercom localisation: Enhancing global communication systems
Date: 10 April 2025
By: Panem Agency
How to perform an SEO audit in less than ten minutes
Think SEO is a nightmare? It doesn't have to be. With the right tools and a list of the key things to look for, you can master your SEO. Here's how.
Date: 9 April 2025 By: Guest post
Seven tips for navigating challenges and staying ahead
The course of business never runs smooth. In this blog, we share seven tips for navigating challenges as they arise.
Date: 24 February 2025 By: Soprano
Virtual IBANs explained
Virtual IBANs offer businesses a flexible, efficient and cost-effective way to accept global payments. In this post, we explain what virtual IBANs are, how they work and how to get a virtual IBAN.
Date: 18 February 2025 By: Mahendra Bajiya
Discover how SEO helps you stay competitive in 2025
SEO helps improve rankings, traffic, and ultimately sales. But, following new SEO trends and techniques matters. Know how to proceed in 2025!
Date: 12 February 2025 By: NinjaReports
Choosing between in-house and outsourced front-end development
Should you use in-house or outsourced front-end development? We compare the pros and cons of each including costs, control and complexity.
Date: 5 February 2025 By: Panem Agency
Manage multi-project resources with scenario analysis software
Simplify the management of multiple projects with scenario analysis software and manage resources more efficiently.
Date: 4 February 2025 By: Panem Agency
Leveraging technology so small businesses can thrive
Small businesses must embrace technology to remain competitive. Here's how monitoring the US Tech 100 can help small businesses keep their finger on the pulse.
Date: 17 January 2025 By: Sarah Mitchell
Best voice recognition solutions for 2025
Voice recognition APIs convert spoken language into text. Here’s how to find the right voice recognition solution for your business and some common uses.
Date: 8 January 2025 By: Rask
Why VoIP is the future of business communication
VoIP gives businesses the tools to streamline workflows, improve customer experiences, and future-proof operations. Discover how it can help your business.
Date: 6 January 2025 By: Kristina Rigina, Kirik
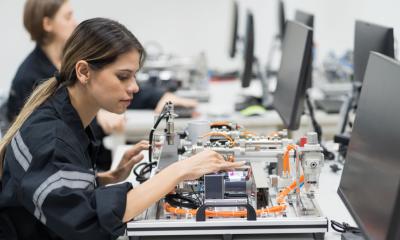
How electronics training can open new careers
Emerging, high-tech sectors require advanced skills. Discover how electronics training can open up new career opportunities.
Date: 2 January 2025 By: Advanced Rework Technology
Custom software development vs. pre-built solutions: Advice for start ups
How do you know whether your start-up business needs customer software development or whether pre-built solutions will suffice? We help you decide.
Date: 20 December 2024 By: Guest post
Cybersecurity tips: protecting your business from online threats
A cybersecurity attack might try to exploit sensitive data, extort money, or prevent businesses from operating normally. Here are six steps to stop cyber criminals in their tracks.
Date: 18 December 2024 By: HostZealot
Using virtual data rooms in mergers and acquisitions
Mergers and acquisitions allow companies to increase value, achieve growth, or expand market share. They involve the exchange of lots of sensitive, financial company data so virtual data rooms can be key.
Date: 1 November 2024 By: Tonya Stevenson
The importance of IT automation tools for small businesses
Small businesses often have to manage with limited budgets and even small teams. Learn how IT automation tools help to streamline business operations and boost workflow for small businesses.
Date: 24 October 2024 By: Atera
Best practice when adopting digital document solutions
Digital document solutions reduce costs, help to automate processes and can help improve security. But, this can only be achieved if the solution is implemented properly. Here’s how to adopt digital document solutions.
Date: 16 October 2024 By: Xenith
Is it time to adopt eSIM technology in your business?
Could eSIMs be the future of mobile communications – especially for those with remote workers and international customers and suppliers?
Date: 10 October 2024 By: ArtSEO SEM
How automated red teaming can improve your cybersecurity
Digital transformation has many undoubted benefits, but it has led to increasingly sophisticated cyber-attacks. Discover how automated red teaming can help you stay one step ahead of the hackers.
Date: 23 September 2024 By: digital-adoption.com
What does the * mean?
If a link has a * this means it is an affiliate link. To find out more, see our FAQs.